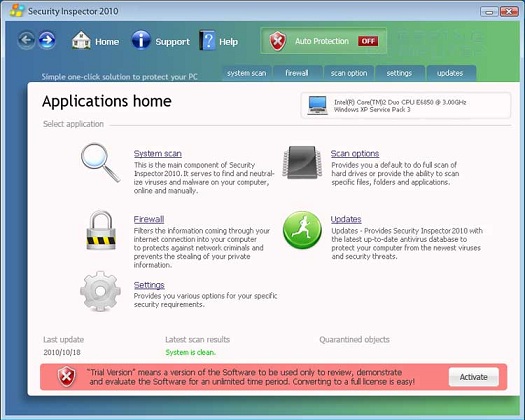
Security Inspector 2010 is a rogue anti-spyware program that is installed via malware without your permission or knowledge. So be careful people because once it is installed it will be configured to start whenever you login to Windows. With your Startup Infected this virus could cause multiple issues with your operating system if not treated immediately. When the Virus starts it will scan your system, prompted that the scan is finished it will state that your computer has numerous amount of virus/malware infections. It will not, though, allow you to remove any of these so-called infections until you first purchase the program. As the detected infections are all fake, you should not purchase the program. Security Inspector 2010 is constantly running and it will also display numerous nag screens and alerts that are designed to make you think your system has a major security issue. These alerts will be shown quite often and will require you to navigate with full attention and all other programs inaccessible through numerous screens before finally closing. Examples of some of the fake security alerts you will encounter while Antivirus Studio is running are:
 Warning!
Warning!
Your computer is being used as spamming machine. You can get sued for spam.
Your computer WILL BE DISCONNECTED FORM INTERNET BECAUSE SPAMMING OTHER PCs
Antivirus Studio Agent
The antivirus database has become outdated and should be updated now. Click on this message to receive the latest antivirus updates.
Program <insert filename here> is infected with virus Generic Dropper.js. Continue running this program may be dangerous to your system and personal data. Running this program can lead to permanent data loss and program instability. Would you like to disinfect this program with antivirus?
Your system might be at risk
Antivirus detects viruses, worms, and Trojan horses. They can (and do) destroy data, format your hard disk or can destroy the BIOS. By destroying the BIOS many times you end up buying a new motherboard or if the bios chip is removable then that chip would need replacing.
Just like the fake alerts, scans, virus, and scan results, these security alerts are all fake and should be completely ignored.
When infected with Security Inspector 2010 your Internet Explorer web browser will also be hijacked to randomly display warnings and infection messages instead the actual web page that you requested. The text of the message is:
Reported Insecure Browsing: Navigation Blocked
Insecure Internet Activity. Threat of virus attack
Due to insecure Internet browsing your PC can easily get infected with viruses, worms, and trojans without your knowledge, and that can lead to system slowdown, freezes and crashes. Also insecure Internet activity can result in revealing your personal information.
This is just another scare tactic being used by the virus program in question and can be completely ignored.
Obviously, Security Inspector 2010 uses scare tactics to get a general computer user into thinking that they have a critical system security problem so that you will purchase the fake program. It goes without having to elaborate any further that you should definitely not purchase Security Inspector 2010 and if you already have, please contact your credit card company and state that the program is a system infection and a scam and hat you would like to dispute the charge. Once the important things are done take a picture of your infected system for our site so we can post it on the wall of shame.
Associated Security Inspector 2010 Files:
%Temp%\_2.tmp
%UserProfile%\Application Data\Microsoft\Internet Explorer\Quick Launch\Security Inspector 2010.lnk
%UserProfile%\Application Data\Security Inspector 2010\
%UserProfile%\Application Data\Security Inspector 2010\Security_Inspector_2010.exe
%UserProfile%\Application Data\Security Inspector 2010\securitycenter.exe
%UserProfile%\Application Data\Security Inspector 2010\securityhelper.exe
%UserProfile%\Application Data\Security Inspector 2010\taskmgr.dll
%UserProfile%\Start Menu\Programs\Security Inspector 2010.lnk
%UserProfile%\Start Menu\Programs\Security Inspector 2010\
%UserProfile%\Start Menu\Programs\Security Inspector 2010\Activate Security Inspector 2010.lnk
%UserProfile%\Start Menu\Programs\Security Inspector 2010\Help Security Inspector 2010.lnk
%UserProfile%\Start Menu\Programs\Security Inspector 2010\How to Activate Security Inspector 2010.lnk
%UserProfile%\Start Menu\Programs\Security Inspector 2010\Security Inspector 2010.lnk
File Location Notes:
%UserProfile% refers to the current user's profile folder. By default, this is C:\Documents and Settings\ for Windows 2000/XP, C:\Users\ for Windows Vista/7, and c:\winnt\profiles\ for Windows NT.
%Temp% refers to the Windows Temp folder. By default, this is C:\Windows\Temp for Windows 95/98/ME, C:\DOCUMENTS AND SETTINGS\ProfileName\LOCAL SETTINGS\Temp for Windows 2000/XP, and C:\Users\ProfileName\AppData\Local\Temp for Windows Vista and Windows 7.
Associated Security Inspector 2010 Windows Registry Information:
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\Security Inspector 2010
HKEY_CURRENT_USER\Software\Security Inspector 2010
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "2kowmeuswvw3"
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "Security Inspector 2010"
HKCU\..\Run: [2kowmeuswvw3] C:\Documents and Settings\Bleeping\Desktop\securetystudio\securetystudio.exe
HKCU\..\Run: [Security Inspector 2010] "C:\Documents and Settings\Bleeping\Application Data\Security Inspector 2010\Security_Inspector_2010.exe" /STARTUP